Solutions > Realtek SoC Security Solutions

Background
Why Realtek Communication ICs Must Fully Enhance Cybersecurity Protection
With the proliferation of the Internet of Things (IoT), smart home devices, and wireless communication equipment, Realtek communication ICs are widely used across a range of end devices and have become key hubs for data transmission.
These devices both process large volumes of users' sensitive data and are increasingly becoming primary targets of cyberattacks.
New‑generation cybersecurity threats include:
- Malware and malicious firmware intrusions.
- Unauthorized remote access and device control.
- Large‑scale Distributed Denial of Service (DDoS) attacks.
- Abuse of weaknesses in communication protocols and implementations.
These trends impose ever‑higher security requirements on communication ICs.

Therefore, strengthening the security mechanisms of Realtek communication ICs is necessary for multiple reasons:
- Prevent hacking and data leakage
By enhancing encryption, authentication, and access‑control mechanisms, the confidentiality and integrity of data in transmission and storage can be effectively protected, preventing sensitive data from being stolen or tampered with.
- Block unauthorized access and malicious control
This helps prevent devices from being exploited as attack platforms or being remotely and illegally controlled, ensuring the security of end devices and network environments.
- Enhance market competitiveness and trust
Providing communication solutions with a high level of security helps earn the trust of customers and partners, and supports compliance with security regulations and certifications (such as PSA and Matter security requirements).
- Protect end users and the broader ecosystem
By establishing security defenses starting from the IC level, overall cybersecurity risks across the supply chain and device life cycle can be significantly reduced.
As cybersecurity threats continue to evolve, security by design has become an essential core capability of Realtek communication ICs, and forms the foundation for long‑term product competitiveness and protection of user information.

Types of Cybersecurity Attacks
Below are common attack types and risks related to IoT/communication ICs:
- Malware and Firmware Implant Attacks
- Malicious firmware updates: attackers exploit update mechanisms to implant malicious firmware, gaining control over devices or stealing data.
- Malicious program execution: attackers exploit software vulnerabilities to inject malicious code, causing the IC to perform unintended behaviors.
- Unauthorized Access
- Weak or default passwords: attackers exploit default or weak passwords to gain access to devices and obtain administrative privileges.
- Breaking authentication flows: attackers exploit protocol vulnerabilities or implementation flaws to bypass login/authentication mechanisms and directly access sensitive data.
- Impersonation and Man‑in‑the‑Middle Attacks (MITM)
Attackers intercept and modify communication between devices, potentially stealing authentication information, decryption keys, or sending forged commands.
- Side‑Channel Attacks
By analyzing the IC's power consumption, electromagnetic emissions, or timing differences during operation, attackers can deduce sensitive information such as encryption keys.
- DDoS and Resource Exhaustion Attacks
Attackers use large amounts of forged packets or connection requests to exhaust CPU, memory, or communication resources, making services unavailable.
- Backdoors and Hardware Vulnerability Exploitation
Attackers exploit reserved or hidden software backdoors, debug interfaces, or hardware weaknesses to covertly control or infiltrate devices.
- Communication Protocol Vulnerability Attacks
Attackers exploit weaknesses in protocol design (e.g., insufficient encryption or incomplete authentication) or in protocol implementations to eavesdrop, tamper with, or forge data streams.

Hardware Protection Technology
Advanced Encryption Standard (AES)
- Feature Overview
- Symmetric block cipher
- AES is a symmetric encryption algorithm where both encryption and decryption use the same key. It operates on 128‑bit (16‑byte) data blocks.
- Multiple key lengths
- Supports 128‑bit, 192‑bit, and 256‑bit key lengths. Longer keys provide stronger security, at the cost of increased computation and resource usage.
- Multi‑round transformation
- Multiple rounds of byte substitution, row shifting, column mixing, and round‑key addition make AES highly resistant to brute‑force and cryptanalytic attacks.
- Application Scenarios
- Encryption of communication data (e.g., data protection within Bluetooth, Wi‑Fi, Ethernet, and other protocols).
- Firmware and storage data encryption (combined with Flash On‑the‑fly Decryption).
- Used together with HASH, TRNG, and Public Key Engine for secure boot, key protection, and secure communication protocols.
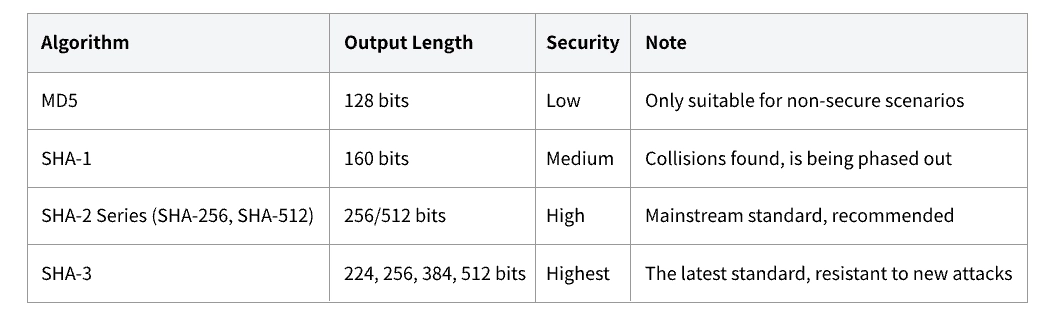
HASH (MD5/SHA)
- Feature Overview
- A hash function is an algorithm that converts input data of any length into a fixed‑length hash value (also called a message digest). It is commonly used to check whether data has been tampered with.
- Irreversibility: it is infeasible to derive the original input from the hash output.
- Collision resistance: it is computationally difficult to find two different inputs that produce the same output.
- Fixed length: regardless of input length, the output length is fixed (for example, SHA‑256 outputs 256 bits).
- MD5 (Message-Digest Algorithm 5)
- Generates a 128-bit (16-byte) hash value.
- Features fast computation speed and low resource consumption.
- Traditionally used for file integrity verification, password storage, and similar applications.
- SHA (Secure Hash Algorithm) Family
- Common versions include SHA-1, SHA-256, and SHA-512.
- SHA-1 generates a 160-bit hash value; SHA-256 generates a 256-bit hash value, and SHA-512 generates a 512-bit hash value.
- A hash function is an algorithm that converts input data of any length into a fixed‑length hash value (also called a message digest). It is commonly used to check whether data has been tampered with.
- Application Scenarios
- Password hashing and verification.
- File/firmware integrity checks.
- Core operations in cryptographic protocols, such as digital signatures and MACs.
- Combined with Secure Boot and Image Encryption to verify that images have not been tampered with.
TRNG
- Feature Overview
- A True Random Number Generator (TRNG) uses physical phenomena (such as thermal noise, circuit jitter, or radioactive decay) to generate digital random numbers. These physical sources are inherently unpredictable, providing high‑quality randomness.
- Outputs cannot be predicted or reproduced by algorithms. Especially suitable for cryptographic keys, one‑time codes, random initialization vectors (IVs), and other security‑critical scenarios.
- Application Scenarios
- Generation of encryption keys (symmetric keys and asymmetric keys such as RSA/ECC).
- One‑time passwords (OTP), random IVs, random challenge values.
- Generation of session keys, nonces, etc. in secure communication protocols, preventing prediction or replay attacks.
Public Key Engine
- Feature Overview
- The Public Key Engine is a dedicated hardware module that accelerates asymmetric cryptography algorithms such as RSA and ECC, greatly reducing the load on the MCU/SoC for signing and verification operations.
- - Supports common public‑key algorithms (e.g., RSA, ECC).
- - Accelerates operations such as key exchange, digital signatures, and signature verification.
- - Works together with Secure Boot, Matter PKI, ARM PSA, and other security frameworks.
- Application Scenario
- Device identity authentication and key exchange (e.g., TLS/Matter/custom security protocols).
- Firmware signature verification (signature checks during Secure Boot).
- Integration with the customer's own PKI (Public Key Infrastructure).
Flash On-the-fly Decryption
- Feature Overview
- Flash On‑the‑fly Decryption allows firmware images stored in external or internal flash to be kept in encrypted form, while the hardware crypto engine decrypts code and data 'on the fly' when the CPU accesses them. There is no need to hold large decrypted images in SRAM.
- Key Features
- Hardware‑accelerated decryption
- The decryption engine is inserted directly between the flash interface and the processor bus, without modifying existing software flows.
- Improved security and usability
- - Prevents unauthorized copying, reverse engineering, or tampering with firmware.
- - Protects algorithms, IP, and sensitive code.
- - Combined with Secure Boot, tampered images cannot be correctly decrypted or booted.
- Application Scenario
- Embedded device firmware protection
- Such as smart appliances, smart speakers, automotive ECUs, industrial control systems, etc.
- IP/algorithm protection
- Encrypt critical algorithms and code before writing to flash, preventing competitors from copying or analyzing them.
- Secure OTA (over‑the‑air) updates
- Only encrypted firmware is written to flash; even if the OTA data is intercepted, it cannot be decrypted.
- Used with Secure Boot to ensure every boot begins from a complete, untampered encrypted image.
ARM TrustZone
- Feature Overview
- ARM TrustZone is a hardware‑level security isolation technology provided by the ARM architecture. It divides system resources into two worlds—'Secure' and 'Non‑secure'—so that system designers can protect confidential data and critical resources.
- Key Features
- Hardware resource isolation
- CPU cores, memory regions, and peripherals can be tagged as Secure or Non‑secure, and hardware ensures isolation between them.
- Dual‑world execution
- - Secure World: runs security‑sensitive tasks, such as key management, cryptographic operations, and authentication services.
- - Non‑secure World: runs general applications and the main OS.
- Secure entry and world switching
- Software must use TrustZone‑controlled secure entry points (Secure Gateways) to access or switch into the Secure World.。
- Enhanced protection and fault isolation
- Even if the Non‑secure World is compromised or infected by malware, hardware separation shields sensitive data and services residing in the Secure World.
- Support for combined security frameworks
- Works with ARM PSA, TEEs, Secure Boot, dynamic lockdown, and other frameworks to enable end‑to‑end security solutions.
- Application Scenario
- Device Key, Password, and Certificate Management
- Sensitive certificates and security keys are stored in the Secure World and can only be accessed by trusted applications (TAs).
- Secure OTA Updates and Firmware Verification
- The update process and image verification are executed within the Secure World to prevent tampering or malicious injection during the OTA process.
- IoT Endpoint Security Enhancement
- Remote commands, configurations, and encrypted data in endpoint devices—such as smart home appliances, industrial control systems (ICS), and automotive devices—are entirely processed within a secure environment.
Security Scheme
Secure Boot
- Feature Overview
- Secure Boot is a mechanism that verifies the integrity and authenticity of a firmware image at power‑on or reset, ensuring that only trusted and unmodified firmware is allowed to execute.
- Key Features
- Prevent execution of malicious firmware or unauthorized software.
- Ensure the boot process starts from a trusted root (Root of Trust).
- Build a complete chain of trust when combined with Image Encryption and the Public Key Engine.
- Hardware-Based Key Protection: Cryptographic keys can be securely stored in non-extractable hardware security regions—such as eFuse, TPM (Trusted Platform Module), or Secure Elements—preventing them from unauthorized extraction or tampering.
- Application Scenarios
- IoT end devices
- Such as smart home, security monitoring, sensors, wearables, etc.
- Smart appliances and embedded products
- Such as smart TVs, speakers, robots, etc.
- Remote firmware update (OTA)
- Verify signatures and integrity of new firmware at post‑update boot.
- Supply‑chain security
- Prevents malicious firmware from being installed at manufacturing, shipping, or deployment stages.
Image Encryption
- Feature Overview
- Image Encryption protects firmware images (firmware, bootloader, application binaries) during storage and transmission.
- Prior to device programming, OTA updates, or mass production, firmware images are encrypted using symmetric (e.g., AES) or asymmetric algorithms. These images reside in flash memory as ciphertext; without the appropriate decryption keys, the contents cannot be deciphered or reverse-engineered.
- Key Features
- Encrypted image storage
- Prevents unauthorized personnel from directly copying, dumping, or examining firmware content.
- Protection against reverse engineering and tampering
- Only systems with the correct keys can decrypt and execute images at boot or load time, effectively protecting algorithms, trade secrets, and sensitive data.
- Hardware–software cooperation
- Typically used with Flash On‑the‑fly Decryption, Secure Boot, and secure key management to ensure the whole firmware execution pipeline is protected.
- Application Scenarios
- Main Program and Model Protection
- Protect main applications and AI models in smart devices (home appliances, in‑car entertainment/navigation units, smart locks, IP cameras, etc.)
- Production and mass‑programming security
- Encrypt images during mass shipping and decrypt only in secure regions on authorized devices.
- Secure OTA updates
- OTA packages remain encrypted end‑to‑end; intercepted or leaked data cannot be reconstructed into usable firmware.
- IP protection and anti‑piracy
- Prevents firmware or software packages from being disassembled or illegally resold.
- Combined with Secure Boot
- Unauthorized image modifications cause verification or decryption failures, providing active protection.
Secure Debug
- Feature Overview
- Traditional Debug Interface Protection
- - During the development phase, the debug interface remains open for convenient programming and debugging.
- - After mass production (MP), the debug interface is closed completely for security, which makes subsequent maintenance or analysis difficult.
- Realtek Secure Debug Management Approach
- Unique Feature: Even after mass production, the Secure Debug mechanism securely authorizes and enables the debug interface, allowing for maintenance and after-sales debugging, while preventing unauthorized access.
- Main Design Highlights
- Password-based Authorization
- The debug interface can only be enabled after password authentication, preventing unauthorized personnel from direct operation.
- Brute-force Protection
- A 'maximum attempt count (Try counter)' is set. If the number of consecutive incorrect password attempts exceeds the limit, the device will be locked and reset, defending against brute-force password attacks.
- Application Scenarios
- Password Input
- The tool (MP Tool) inputs the password via UART to the system's AON Register.
- Boot Process (Secure Boot)
- Upon device startup, the Secure Boot process verifies debug authorization.
- Read Try Counter
- Reads the 'Try counter' from OTP. If the counter has reached zero, the system is immediately reset, and no further attempts are allowed.
ARM Platform Security Architecture (ARM PSA)
- Feature Overview
- PSA (Platform Security Architecture) is a comprehensive security standard and framework introduced by ARM to enhance the security of IoT and embedded endpoint devices. PSA provides an end‑to‑end security solution that includes design guidelines, API specifications, and certification procedures, covering security requirements from hardware and software to system integration.
- Key Features
- Security design process and architectural guidelines
- - Threat modeling
- - Attack surface minimization
- - Best‑practice guidelines for secure design
- Standardized security APIs
- - Hardware Root of Trust (RoT)
- - Secure storage, cryptography, and key management
- - Device authentication APIs (e.g., PSA Crypto API)
- - These make software more portable and interoperable.
- Layered security model. Clearly distinguishes between
- Root of Trust (RoT), Security Services, Application layer. This helps architects and developers build layered defenses.
- Security certification
- Through PSA Certified, third‑party labs can evaluate whether SoCs, firmware, and platforms meet PSA security requirements, making it easier for the ecosystem to adopt these products.
- Application Scenarios
- IoT Endpoint Security Design
- Enables rapid adoption of PSA security solutions for endpoint encryption and user identity/firmware authentication (UIFA) in smart home and industrial sensor devices.
- Device Authentication and Root of Trust Management
- Effectively manages device identities with PSA-RoT (Platform Root of Trust), enhancing supply chain trust and anti-counterfeiting capabilities.
- Secure OTA Firmware Updates
- Uses PSA-provided certification and cryptographic APIs to ensure firmware upgrade processes are protected from forgery or malicious tampering.
- Device Development for Regulatory Compliance
- PSA Certified serves as an implementation basis for highly regulated industries (finance, automotive, medical), helping speed up industry security certifications.
Matter Public Key Infrastructure (PKI)
- Feature Overview
- Matter PKI is the public key infrastructure within the Matter smart‑home standard (initiated by the CSA). It manages device identities, secure encrypted communications, and device authentication. Based on X.509 certificates, public/private key pairs, and related technologies. Ensures identity authentication, data integrity, and confidentiality for all communications between Matter devices
- Key Features
- Device identity management
- Assigns each Matter device a unique device certificate for authentication and trust‑chain management.
- Secure communication setup
- Devices validate each other via certificates and public keys, then establish encrypted channels to prevent eavesdropping and MITM attacks.
- Device authentication and authorization
- Core Matter flows (such as pairing and network onboarding) rely on PKI‑based identity checks, allowing only authorized devices to participate.
- Supply chain security
- Certificates are programmed during manufacturing via PKI, so devices ship with verifiable identities, effectively reducing the risk of counterfeit devices entering the market.
- Hierarchical trust management
- Supports brand‑owned root CAs, intermediate CAs, and third‑party CAs (e.g., CSA‑approved authorities), enabling hierarchical control for large‑scale deployments.
- Application Scenarios
- Smart Home Device Pairing and Network Formation
- When users add new devices (e.g., bulbs, outlets) to the Matter network, PKI-based authentication validates device identity, blocking counterfeit or unauthorized devices.
- Cross-brand Smart Device Interoperability
- Devices from different manufacturers and categories (such as Apple HomePod, Amazon Echo, Samsung smart bulbs) can establish secure connections within the same Matter network based on PKI trust.
- Firmware Upgrade Security
- Prior to accepting OTA firmware updates, devices verify that the update package is signed by a trusted vendor, preventing malicious code injection.
- Supply Chain and Inventory Anti-counterfeiting
- Devices can be PKI-authenticated throughout production, logistics, and into consumer hands, strengthening trust and legitimacy across the entire supply chain.
- Securing Remote Control and Access
- When users control Matter devices remotely (via mobile apps or voice assistants), PKI ensures each command originates from a legitimate, authorized controller.
Certificate-based Authentication and Pairing
- Feature Overview
- Certificate‑based authentication and pairing for Bluetooth is designed to improve security, mutual trust, and user experience. Unlike traditional PIN/SMP (Simple Pairing) methods, this mechanism uses PKI (Public Key Infrastructure) and digital certificates to authenticate device identities and establish encrypted links.
- Key Features
- Device Identity Authentication
- Utilizes digital certificates (e.g., X.509) to verify whether a Bluetooth device is from a legitimate and authorized source, preventing counterfeit or unauthorized device impersonation.
- Secure Pairing Process
- The pairing process not only compares certificates but also uses key exchange (such as ECDH) to generate a session key, ensuring communication confidentiality and tamper resistance.
- Dynamic Trust Management
- Bluetooth pairing certificates can be managed and issued by brand Root CA, intermediate CA, or third-party authorities (e.g., Bluetooth SIG), making large-scale or enterprise device management more flexible.
- Support for Advanced Security Standards
- In addition to standard pairing, it supports advanced modes like LE Secure Connections, Just Works, or Passkey Entry, meeting stringent IoT, automotive, or wearable device security needs.
- Application Scenarios
- Enterprise/Medical Device Secure Pairing
- In environments such as hospitals, Bluetooth sensors and stethoscopes must securely pair so that only authorized instruments join the network, protecting against eavesdropping or interference from unauthorized devices.
- Automotive Bluetooth Connectivity
- Vehicle Bluetooth modules (e.g., keyless entry, head units) mutually authenticate using certificates, preventing impersonation or unauthorized devices from illegally unlocking or operating vehicle systems.
- Smart Home/Access Control Systems
- Home Bluetooth door locks or access systems utilize certificate-based hierarchical access (admin/general user), ensuring that only authorized phones or cards can unlock doors.
- Advanced IoT Device Interoperability
- In multi-vendor Bluetooth networks, devices can authenticate each other's identities through certificate exchange, reducing risks of impersonation or attacks while improving interoperability reliability.
- Mass Production Device Supply Chain Management
- Device certificates can be embedded during manufacturing, enabling instant end-user authentication upon shipment, eliminating the need for manual PIN or password input at the deployment site.
Part Number Comparison Table
| Function/Part number | BLESoC | BTSoC | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| RTL87x2C | RTL87x2D | RTL87x2E | RTL87x2H | RTL87x2G | RTL8763E | RTL8773C | RTL87x3D | RTL8773E | RTL87x3G | |||
| Hardware Security IP | AES | 128bits | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ |
| 256bits | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✗ | ✗ | ✓ | ✓ | ||
| SHA | SHA256 | ✗ | ✗ | ✗ | ✓ | ✓ | ✗ | ✓ | ✓ | ✓ | ✓ | |
| TRNG | ✗ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ||
| PKE | ECC | ✗ | ✗ | ✗ | ✗ | ✓ | ✗ | ✗ | ✓ | ✓ | ✓ | |
| RSA | ✗ | ✗ | ✗ | ✗ | ✓ | ✗ | ✗ | ✓ | ✓ | ✓ | ||
| Trustzone | ✗ | ✗ | ✗ | ✗ | ✓ | ✗ | ✗ | ✗ | ✗ | ✗ | ||
| Flash On-The-Fly Decryption | ✗ | ✗ | ✗ | ✓ | ✓ | ✗ | ✗ | ✗ | ✗ | ✓ | ||
| OTP Size (Bits) | 4096 | 4096 | 512 | 5120 | 8192 | 4096 | 8192 | 65536 | 4096 | 4096 | ||
| Security Scheme | Secure Boot | ✓ | ✓ | ✗ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| Image Encryption | ✓ ¹ | ✓ ¹ | ✓ ¹ | ✓ ² | ✓ ² | ✓ ¹ | ✓ | ✓ ¹ | ✓ ¹ | ✓ | ||
| Secure Debug | ✓ | ✓ | ✗ | ✓ | ✓ | ✗ | ✓ | ✓ | ✗ | ✓ | ||
| ARM PSA (Platform Security Architecture) Certified | (PSA Level 1) ³ | PSA Level 1 | N | (PSA Level 1) ³ | PSA Level 2 | PSA Level 1 | (PSA Level 1) ³ | (PSA Level 1) ³ | (PSA Level 1) ³ | (PSA Level 1) ³ | ||
- Note 1: Image decryption through copy to memory. It will occupy additional SRAM for the decrypted image.
- Note 2: Image decryption through Flash on the Fly.
- Note 3: Platform is ready for the PSA Level 1.



 苏公网安备32059002006558号
苏公网安备32059002006558号